Microsoft on Tuesday disclosed that a large-scale phishing
campaign targeted over 10,000 organizations since September 2021 by
hijacking Office 365’s authentication process even on accounts
secured with multi-factor authentication (MFA).
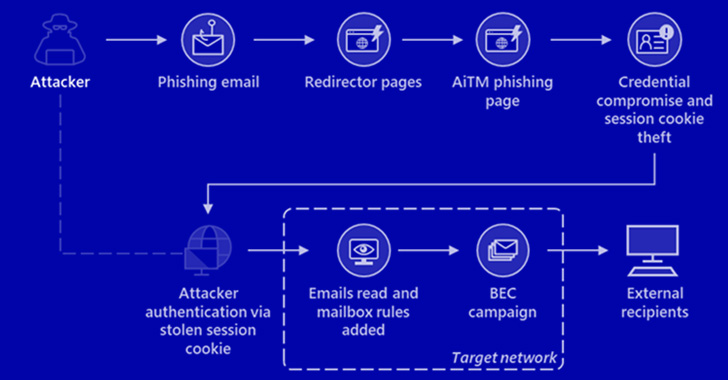
“The attackers then used the stolen credentials and session
cookies to access affected users’ mailboxes and perform follow-on
business email compromise (BEC) campaigns against other targets,”
the company’s cybersecurity teams reported[1].
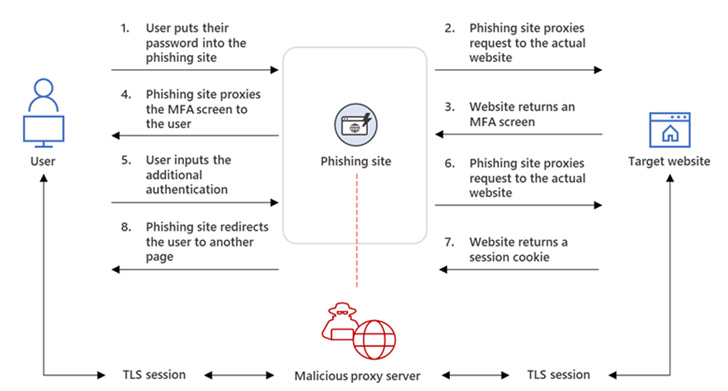
The intrusions entailed setting up adversary-in-the-middle
(AitM) phishing sites, wherein the adversary deploys a proxy server
between a potential victim and the targeted website so that
recipients of a phishing email are redirected to lookalike landing
pages designed to capture credentials and MFA information.
“The phishing page has two different Transport Layer Security
(TLS) sessions — one with the target and another with the actual
website the target wants to access,” the company explained.
“These sessions mean that the phishing page practically
functions as an AitM agent, intercepting the whole authentication
process and extracting valuable data from the HTTP requests such as
passwords and, more importantly, session cookies.”
Armed with this information, the attackers injected the cookies
into their own browsers to circumvent the authentication process,
even in scenarios where the victim had enabled MFA protections.
The phishing campaign spotted by Microsoft was orchestrated to
single out Office 365 users by spoofing the Office online
authentication page, with the actors using the Evilginx2 phishing
kit for carrying out the AitM attacks.
This involved sending email messages containing voice
message-themed lures that were marked with high importance,
tricking the recipients into opening malware-laced HTML attachments
that redirected to the credential-stealing landing pages.
To complete the ruse, the users were eventually redirected to
the legitimate office[.]com website post-authentication, but not
before the attackers leveraged the aforementioned AitM approach to
siphon the session cookies and obtain control over the compromised
account.
The attacks didn’t end there, for the threat actors abused their
mailbox access to perform payment fraud by using a technique called
email thread hijacking to dupe parties on the other end of the
conversation to illicitly wire funds to accounts under their
control.
To further mask their communications with the fraud target, the
threat actors also created mailbox rules that automatically moved
every incoming email containing the relevant domain name to the
“Archive” folder and marked it as “read.”
“It took as little time as five minutes after credential and
session theft for an attacker to launch their follow-on payment
fraud,” Microsoft noted.
The attackers are said to have employed Outlook Web Access (OWA)
on a Chrome browser to conduct the fraudulent activities, while
also deleting from the account’s Inbox folder the original phishing
email as well as the follow-on communications with the target from
both the Archive and Sent Items folders to erase traces.
“This AiTM phishing campaign is another example of how threats
continue to evolve in response to the security measures and
policies organizations put in place to defend themselves against
potential attacks,” the researchers said.
“While AiTM phishing attempts to circumvent MFA, it’s important
to underscore that MFA implementation remains an essential pillar
in identity security. MFA is still very effective at stopping a
wide variety of threats; its effectiveness is why AiTM phishing
emerged in the first place.”
The findings come as a group of researchers from Stony Brook
University and Palo Alto Networks demonstrated late last year a new
fingerprinting technique that makes it possible to identify AitM
phishing kits in the wild using a tool called PHOCA[2].
Read more https://thehackernews.com/2022/07/microsoft-warns-of-large-scale-aitm.html