Often, organizations think of firewall security as a
one-and-done type of solution. They install firewalls, then assume
that they are “good to go” without investigating whether or not
these solutions are actually protecting their systems in the best
way possible. “Set it and forget it!”
Instead of just relying on firewalls and assuming that they will
always protect their businesses from cyber risk, executives need to
start asking deeper questions about them. As with most areas of
business, it’s important to take a critical look at each solution
that your organization relies on for security. So, let’s break down
a few questions that you and your team should be asking about
firewall security to get a more accurate view into your network
defense posture.
1 — What does your team’s firewall knowledge look
like?
In order to properly service and upkeep firewalls, your team
needs to have at least a baseline knowledge of how firewalls
operate. It’s especially important to understand what a firewall
can and can’t do. For instance, next-generation firewall solutions
are built to perform deep packet inspection, meaning they look into
individual pieces of information that enter and exit your system –
a “gatekeeper” for your systems, per se. They perform this function
well, but only when they can actually see the data in the payload.
This is becoming more and more difficult in the age of
“encrypt-everything”.
2 — Does your security team spend time understanding the
“other side”?
Who is on the other side of malicious attacks? In order to
understand how to safeguard your network from harm, your team needs
to understand what – and who – they’re defending against. The
landscape of cyber-attacks has drastically changed over the past
few years, and malicious actors have accelerated in skill. With the
advancement in technologies comes more efficient and dangerous
cyber-criminals.
Hackers in the 2020s have more powerful tools than ever before,
literally at their fingertips. They’re intelligent people, driven
by tools that cost them little to nothing to obtain. As an example,
credential stuffing attacks (taking a username and password from
one site, and trying it out on other sites to access additional
credentials) can be executed easily with a free, open-source tool
called OpenBullet[1].
Security teams need to take all of this into account, as they
consider their existing firewall solutions. They also need to
consider the fact that most next-generation firewall solutions
pre-date many of these powerful hacking tools by 10-20 years, and
have changed little over the past two decades.
3 — Can your next-generation firewall solution really
encrypt and de-encrypt all of your data?
Unlike 20 years ago, when firewalls were first introduced,
almost all data packets that travel in and out of systems are
encrypted. This means that in order for deep packet inspection to
work, your firewall needs to be able to de-encrypt the data, look
through the contents for any indications of malicious activity, and
then, in many situations, re-encrypt them to adhere to modern-day
compliance standards.
This can take an enormous amount of processing power and time,
so your firewall solution not only needs to have the capability to
encrypt and de-encrypt, but your system needs to have the bandwidth
to support these activities. Worse, modern encryption techniques
driven by the global demand for privacy, are making it more and
more difficult to decrypt and re-encrypt data in the first
place.
4 — How many IP addresses can your firewall solution
block?
As we’ve explored above, deep packet inspection in a world of
encrypted data can be a time-consuming process, which can then
become a roadblock for today’s fast-paced network environments. And
because of this, your firewall technology should have a way to
complement deep packet inspections, in case de-encryption can’t
happen in time and packets containing malicious payloads slip
through the cracks.
The best way to ensure that nothing gets past your firewall
unnoticed? By implementing IP address filtering as well. Since all
traffic is identified by a unique IP address, it’s a simple way to
catch any packets coming from (or going to) known malicious
locations and block them, without even needing to check their
contents.
But there’s an unfortunate reality about IP address filtering:
most well-known firewall security vendors cite that their solutions
can only recognize and block around 100,000-1 million IP addresses,
at the very most. There are millions (or billions) of known bad IP
circulating in the world right now. That’s crazy, right?! We
thought so too, and created ThreatBlockr[2]
as a solution that solely focused on IP address blocking to fill
this evident gap. Our solution can support up to 150 million IPs
and Domains – about 1,000 times more than firewalls can support.
This is because we designed ThreatBlockr specifically for this use
case. Firewalls weren’t built for this use case – they were built
for deep packet inspection, which is a very different engineering
problem.
5 — Is your team supplementing your firewall solution with
other security practices?
As powerful as firewall solutions can be, they are only as
strong as the humans at your organization. No matter how vigilant
and advanced your security team’s initiatives are, if a single
employee clicks on a phishing email link, those efforts could all
be for nothing.
It’s important to consider cybersecurity awareness training,
right alongside security solutions such as firewalls. When your
employees can avoid phishing schemes and create (and rotate) secure
passwords, they will contribute positively to your overall security
program, making your purchased solutions all the more effective.
When your IT team is rigorous about the timely installation of the
latest software security patches across your entire business
software ecosystem, your security posture will improve
immensely.
The bottom line: firewalls aren’t a magical, black box solution
that can fix all security flaws. Firewalls are clearly not a silver
bullet. If they were, no one would be getting hacked. Yet, here we
are, in 2022, with new breaches and threats identified every day.
Firewalls have their place in a security team’s toolkit but need to
be complemented with gap-filling solutions, methodologies, and
company-wide best practices. Only then can effective cyber security
truly be realized.
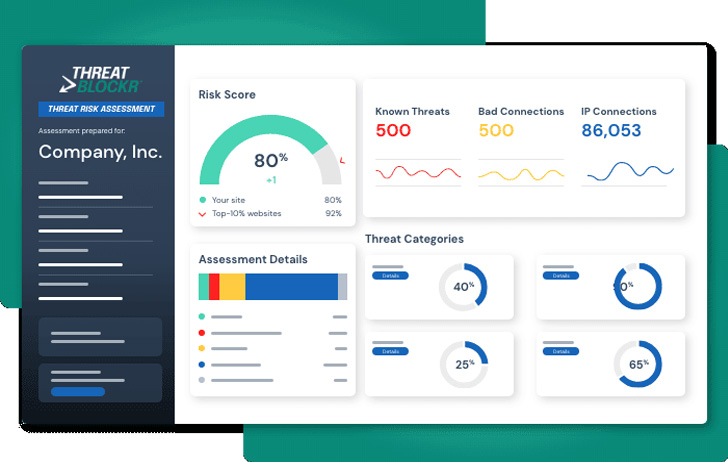
For organizations looking to understand what threats are getting
through their existing security stacks, ThreatBlockr offers a
free threat risk assessment[3] to get a comprehensive
network security audit.
References
- ^
OpenBullet
(www.ijstr.org) - ^
ThreatBlockr
(www.threatblockr.com) - ^
free
threat risk assessment
(www.threatblockr.com)
Read more https://thehackernews.com/2022/07/5-questions-you-need-to-ask-about-your.html