Cybersecurity researchers have uncovered new variants of the
ChromeLoader[1]
information-stealing malware, highlighting its evolving feature set
in a short span of time.
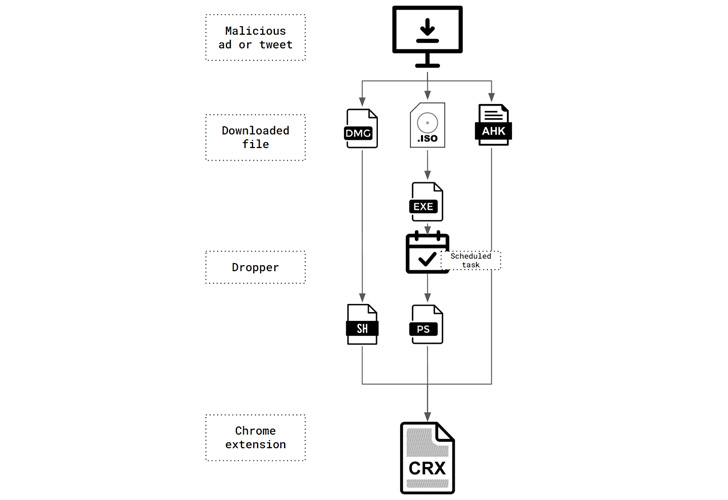
Primarily used for hijacking victims’ browser searches and
presenting advertisements, ChromeLoader came to light in January
2022 and has been distributed in the form of ISO or DMG file
downloads advertised via QR codes on Twitter and free gaming
sites.
ChromeLoader has also been codenamed Choziosi Loader and
ChromeBack by the broader cybersecurity community. What makes the
adware notable is that it’s fashioned as a browser extension as
opposed to a Windows executable (.exe) or Dynamic Link Library
(.dll).
Besides requesting invasive permissions to access browser data
and manipulate web requests, it’s also designed to capture users’
search engine queries on Google, Yahoo, and Bing, effectively
allowing the threat actors to harvest their online behavior.
While the first Windows variant of ChromeLoader malware was
spotted in January, a macOS version of the malware emerged in March
to distribute the rogue Chrome extension (version 6.0) in the form
of disk image (DMG) files.
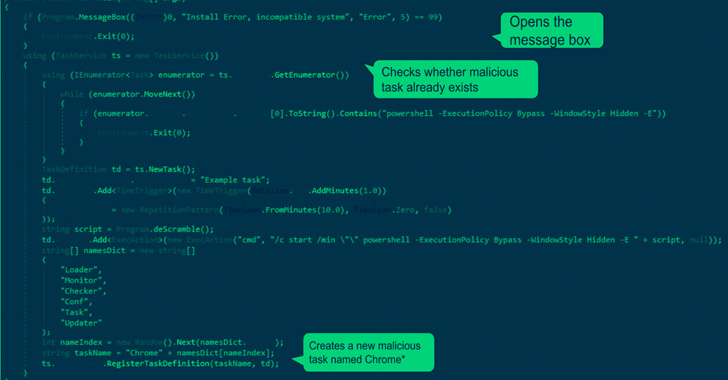
But a new analysis from Palo Alto Networks Unit 42 indicates[2]
that the earliest known attack involving the malware occurred in
December 2021 using an AutoHotKey-compiled executable in place of
the later-observed ISO files.
“This malware was an executable file written using AutoHotKey
(AHK[3]) — a framework used for
scripting automation,” Unit 42 researcher Nadav Barak said, adding
it was used to drop “version 1.0” of the browser add-on.
This first version is also said to lack obfuscation
capabilities, a feature that has been picked up in subsequent
iterations of the malware to conceal its purpose and malicious
code.
Also observed in March 2022 was a previously undocumented
campaign using the 6.0 version of the Chrome extension and relies
on an ISO image that contains a seemingly benign Windows shortcut,
but, in reality, acts as a conduit to launch a hidden file in the
mounted image which deploys the malware.
“This malware demonstrates how determined cybercriminals and
malware authors can be: In a short time period, the authors of
ChromeLoader released multiple different code versions, used
multiple programming frameworks, enhanced features, advanced
obfuscators, fixed issues, and even adding cross-OS support
targeting both Windows and macOS,” Barak said.
References
Read more https://thehackernews.com/2022/07/researchers-uncover-new-variants-of.html