The operators behind the Qakbot malware are transforming their
delivery vectors in an attempt to sidestep detection.
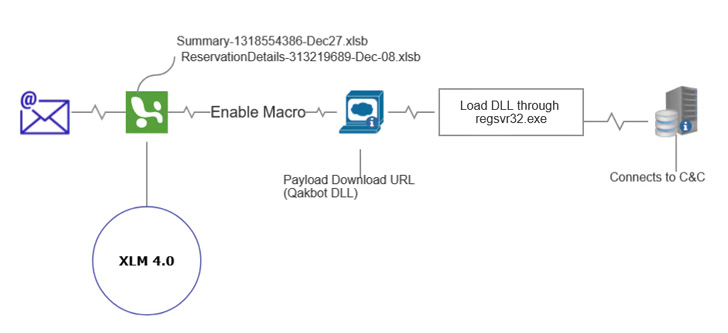
“Most recently, threat actors have transformed their techniques
to evade detection by using ZIP file extensions, enticing file
names with common formats, and Excel (XLM) 4.0 to trick victims
into downloading malicious attachments that install Qakbot,”
Zscaler Threatlabz researchers Tarun Dewan and Aditya Sharma
said[1].
Other methods adopted by the group include code obfuscation,
introducing new layers in the attack chain from initial compromise
to execution, and using multiple URLs as well as unknown file
extensions (e.g., .OCX, .ooccxx, .dat, or .gyp) to deliver the
payload.
Also called QBot, QuackBot, or Pinkslipbot, Qakbot has been a
recurring threat[2]
since late 2007, evolving from its initial days as a banking trojan
to a modular information stealer capable of deploying next-stage
payloads such as ransomware[3].
“Qakbot is a flexible post-exploitation tool that incorporates
various layers of defense evasion techniques designed to minimize
detections,” Fortinet disclosed[4]
in December 2021.
“Qakbot’s modular design and infamous resiliency in the face of
traditional signature-based detection make it a desirable first
choice for many financially motivated groups (cyber
criminals).”
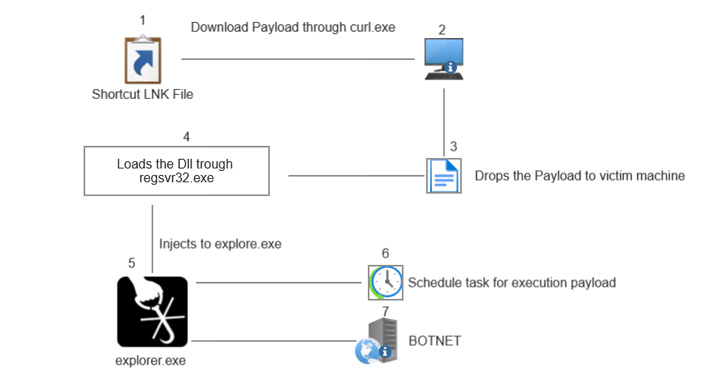
The shifting tactics adopted by the malware from XLM macros in
early 2022 to .LNK files in May is seen as an attempt to counter
Microsoft’s plans to block Office macros by default in April 2022,
a decision it has since temporarily rolled back[5].
In addition, further modifications include the use of PowerShell
to download the DLL malware and a switch from regsvr32.exe to
rundlll32.exe to load the payload, in what the researchers
described as a “clear sign of Qakbot evolving to evade updated
security practices and defenses.”
References
- ^
said
(www.zscaler.com) - ^
recurring threat
(thehackernews.com) - ^
ransomware
(thehackernews.com) - ^
disclosed
(www.fortinet.com) - ^
temporarily rolled back
(thehackernews.com)
Read more https://thehackernews.com/2022/07/researchers-uncover-new-attempts-by.html