Cloud security is the umbrella that holds within it: IaaS, PaaS
and SaaS. Gartner created the SaaS Security Posture Management
(SSPM) category for solutions that continuously assess security
risk and manage the SaaS applications’ security posture. With
enterprises having 1,000 or more employees relying on dozens to
hundreds of apps, the need for deep visibility and remediation for
SaaS security settings is only getting more critical.
The top pain points for SaaS security stem from:
- Lack of control over the growing SaaS app
estate - Lack of governance in the lifecycle of SaaS
apps: from purchase to deployment, operation and maintenance - Lack of visibility of all the configurations
in SaaS app estate - Skills gap in ever-evolving, accelerating,
complex cloud security - Laborious and overwhelming workload to stay on
top of hundreds to thousands (to tens of thousands) of settings and
permissions.
The capability of governance across the whole SaaS estate is
both nuanced and complicated. While the native security controls of
SaaS apps are often robust, it falls on the responsibility of the
organization to ensure that all configurations are properly set —
from global settings, to every user role and privilege. It only
takes one unknowing SaaS admin to change a setting or share the
wrong report and confidential company data is exposed. The security
team is burdened with knowing every app, user and configuration and
ensuring they are all compliant with industry and company
policy.
Effective SSPM solutions come to answer these pains and provide
full visibility into the company’s SaaS security posture, checking
for compliance with industry standards and company policy. Some
solutions even offer the ability to remediate right from within the
solution. As a result, an SSPM tool can significantly improve
security-team efficiency and protect company data by automating the
remediation of misconfigurations throughout the increasingly
complex SaaS estate.
As one might expect, not all SSPM solutions are created equal.
Monitoring, alerts, and remediation should sit at the heart of your
SSPM solution. They ensure that any vulnerabilities are quickly
closed before they are exploited by cyberattacks. Solutions like
the one developed by Adaptive Shield create a window into the SaaS
environment. When comparing SSPM options, here are some key
features to look out for (excerpted from the complete guide[1]).
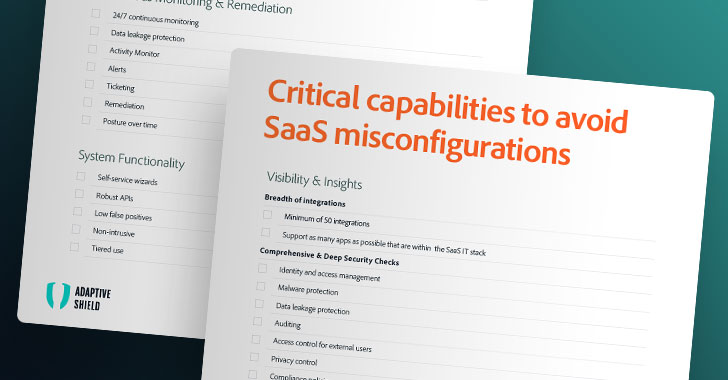
Visibility & Insights
Run comprehensive security checks to get a clear look into
your SaaS environment, at all the integrations, and all the domains
of risk.
Breadth of integrations
First and foremost for an SSPM solution, is the SSPM’s ability
to integrate with all your SaaS apps. Each SaaS has its own
framework and configurations, if there is access to users and the
company’s systems, it should be monitored by the organization. Any
app can pose a risk, even non-business-critical apps. Point of note
is that often smaller apps can serve as a gateway for an
attack.
- Look for an SSPM system with a minimum of 30 integrations that
are adaptable and able to run checks on every data type to protect
against misconfigurations. - Even more, a solution should be able to support as many apps as
possible that are within the SaaS IT stack, in a seamless
“out-of-the box” way.
Comprehensive & Deep Security Checks
The other vital component to an effective SSPM is the expanse
and depth of the security checks. Each domain has its own facets
for the security team to track and monitor.
- Identity and access management
- Malware protection
- Data leakage protection
- Auditing
- Access control for external users
- Privacy control
- Compliance policies, security frameworks and benchmarks
Get the complete guide along with the
printable checklist here.[2]
Continuous Monitoring & Remediation
Combat threats with continuous oversight and fast
remediation of any misconfiguration
Remediating issues in business environments is a complicated and
delicate task. The SSPM solution should provide deep context about
each and every configuration and enable you to easily monitor and
set up alerts. This way vulnerabilities are quickly closed before
they are exploited by cyberattacks.
SSPM vendors like Adaptive Shield provide you with these tools,
which allow your security team to communicate effectively, shut
down vulnerabilities, and protect your system.
- 24/7 continuous monitoring
- Activity Monitor
- Alerts
- Ticketing
- Remediation
- Posture over time
System Functionality
Integrate a strong and smooth SSPM system, without extra
noise.
Your SSPM solution should be easy to deploy and allow your
security team to easily add and monitor new SaaS applications. Top
security solutions should integrate easily with your applications
and your existing cybersecurity infrastructure, to create a
comprehensive defense against cyber threats.
- Self-service wizards
- Robust APIs
- Low false positives
- Non-intrusive
- Tiered use
Final Thoughts
The Right SSPM solution PREVENTS Your next attack
SSPM is similar to brushing one’s teeth: it’s a foundational
requirement needed to create a preventative state of protection.
The right SSPM, like Adaptive Shield, provides organizations
continuous, automated surveillance of all SaaS apps, alongside a
built-in knowledge base to ensure the highest SaaS security
hygiene.
Using Adaptive Shield, security teams will deploy best practices
for SaaS security, while integrating with all types of SaaS
applications—including video conferencing platforms, customer
support tools, HR management systems, dashboards, workspaces,
content, file-sharing applications, messaging applications,
marketing platforms, and more.
Adaptive Shield’s framework is easy to use, intuitive to master,
and takes five minutes to deploy.
Learn more about how you can secure your
company’s SaaS security now.[3]
References
- ^
the
complete guide (go.adaptive-shield.com) - ^
Get the
complete guide along with the printable checklist here.
(go.adaptive-shield.com) - ^
Learn
more about how you can secure your company’s SaaS security now.
(www.adaptive-shield.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/N2XECtZqn_o/the-ultimate-saas-security-posture.html