China-linked adversaries have been attributed to an ongoing
onslaught against Indian power grid organizations, one year after a
concerted campaign[1]
targeting critical infrastructure in the country came to light.
Most of the intrusions involved a modular backdoor named
ShadowPad[2], according to Recorded
Future’s Insikt Group, a sophisticated remote access trojan which
has been dubbed[3]
a “masterpiece of privately sold malware in Chinese espionage.”
“ShadowPad continues to be employed by an ever-increasing number
of People’s Liberation Army (PLA) and Ministry of State Security
(MSS)-linked groups, with its origins linked to known MSS
contractors first using the tool in their own operations and later
likely acting as a digital quartermaster,” the researchers said[4].
The goal of the sustained campaign, the cybersecurity company
said, is to facilitate intelligence gathering pertaining to
critical infrastructure systems in preparation for future
contingency operations. The targeting is believed to have commenced
in September 2021.
The attacks took aim at seven State Load Despatch Centres
(SDLCs) located primarily in Northern India, in particular those
close to the disputed India-China border in Ladakh, with one of the
targets victimized in a similar attack disclosed in February 2021
and attributed to the RedEcho group.
The 2021 RedEcho attacks involved the compromise of 10 distinct
Indian power sector organizations, including six of the country’s
regional and state load despatch centres (RLDC), two ports, a
nation power plant, and a substation.
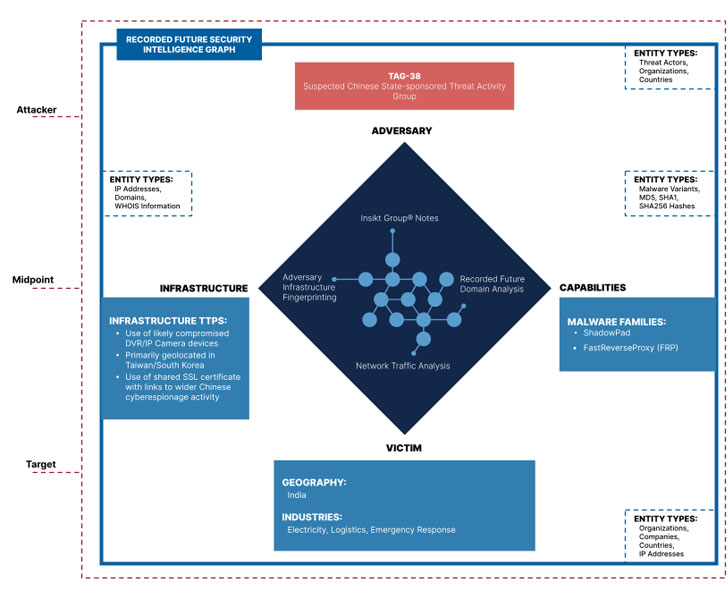
Recorded Future linked the latest set of malicious activities to
an emerging threat cluster it’s tracking under the moniker Threat
Activity Group 38 aka TAG-38 (similar to the UNC####[5]
and DEV-#### designations given by Mandiant and Microsoft), citing
“notable distinctions” from that of the previously identified
RedEcho TTPs.
In addition to attacking power grid assets, TAG-38 impacted a
national emergency response system and the Indian subsidiary of a
multinational logistics company.
Although the initial infection vector used to breach the
networks is unknown, the ShadowPad malware on the host systems were
commandeered by means of a network of infected internet-facing
DVR/IP camera devices geolocated in Taiwan and South Korea.
“The use of ShadowPad across Chinese activity groups continues
to grow over time, with new clusters of activity regularly
identified using the backdoor as well as continued adoption by
previously tracked clusters,” the researchers said, adding it’s
monitoring at least 10 distinct groups with access to the
malware.
Following the disclosure, India’s Union Power Minister R. K.
Singh characterized[6]
the intrusions as unsuccessful “probing attempts” at hacking which
happened in January and February, and that the government is
constantly reviewing its cybersecurity mechanisms to bolster
defenses.
China, for its part, reiterated[7]
that it “firmly opposes and combats all forms of cyber attacks” and
that “cybersecurity is a common challenge facing all countries that
should be jointly addressed through dialogue and cooperation.”
“Recently, Chinese cybersecurity companies released[8]
a series of reports[9], revealing that the U.S.
government launched cyber attacks on many countries around the
world, including China, seriously jeopardizing the security of
critical infrastructure of these countries,” China’s Foreign
Ministry spokesperson, Zhao Lijian, said[10].
“It is worth noting that many of U.S. allies or countries with
which it cooperates on cyber security are also victims of U.S.
cyber attacks. We believe that the international community,
especially China’s neighboring countries, will keep their eyes wide
open and make their own judgment on the true intentions of the U.S.
side.”
References
- ^
concerted campaign
(thehackernews.com) - ^
ShadowPad
(thehackernews.com) - ^
dubbed
(thehackernews.com) - ^
said
(www.recordedfuture.com) - ^
UNC####
(www.mandiant.com) - ^
characterized
(www.youtube.com) - ^
reiterated
(www.fmprc.gov.cn) - ^
released
(thehackernews.com) - ^
series
of reports (www.scmp.com) - ^
said
(www.fmprc.gov.cn)
Read more https://thehackernews.com/2022/04/chinese-hacker-groups-continue-to.html